Have you ever used the location on your computer? I bet you have : Mac OS X have been integrating Core Location since Snow Leopard and OS X Mavericks will integrate Maps. On Google Maps, a small button can be used to get located directly on a map, and it usually works pretty well. But de you have an idea of how it works and do you know it’s pretty easy to completely distort this location?
Before starting, here is a small video of the result: Google Maps gets lost when I run my program on the Raspberry Pi.
How does it work?
Let’s start with a little history: your unit has a GPS receiver. It will therefore use different satellites to triangulate: the distance between you and the satellites is known, then it is fairly simple to position yourself on a map. The problem is that it is quite slow, capturing different satellites can take several minutes.
To solve this problem, smartphones have built a technology that allows you to quickly locate, using two different techniques.
The first one is a location using the antennas of the mobile network. This is the technique used in movies (and reality) to find missing persons. The principle is simple: the exact position of the antenna is known and we can calculate (estimate, in fact) the distance between the antenna and your device, which is used to triangulate a position. It is not very accurate – there are hardly many visible antennas and the distance is estimated crudely – but it’s enough for some services such as management of time zones, weather, etc.. Another concern of this technique, you need a device with a GSM chip.
The second method, found in computers, tablets and smartphones, uses the Wi-Fi networks. The principle remains the same: a triangulation of the position via Wi-Fi networks. It is often more efficient than the mobile network: it is not uncommon to catch a dozen different Wi-Fi networks. There are three different bases: Skyhook (used by Apple in older versions of iOS), Google (built with the Street View vehicles), and Apple (built in crowdfunding from iOS devices and used since iOS 4).
On a Mac, Firefox and Chrome use the Google base, and other applications (Safari, Maps in Mavericks, etc..) use the Apple base through the Core Location integrated on the OS.
The problems…
Before talking about the attack, we can talk about false positives. The most common case – it happened to me – is the move: if you move your Wi-Fi Hotspot, the bases of operators are simply outdated. And if there is little Wi-Fi network, the location will be distorted: your access point remains located at the previous address, the location will consider that you have not moved. The solution – at least for Apple – is to connect a device with a physical GPS (iPhone, iPad 3G), launch Maps, enable Wi-Fi and wait. Apple’s base is updated periodically, taking into account the data returned by iOS devices and if your iPhone captures your networks, the base will be updated with the correct position, more or less rapidly.
The second case of false positives, is 3G routers (MiFi): bases can reference them, whereas they do not have a fixed position. There is no solution to my knowledge to avoid referencing on Apple, while Google offers to add _nomap at the end of the name of the network to remove the router base.
… and attack
You may be wondering what I am up to: if the location uses Wi-Fi networks .. then just create fake wireless networks. The modus operandi is not new: in 2008, a paper explained how to twist the results and in 2011, a hacker showed a video of the attack. I just simplified things by using a Raspberry Pi and a standard Wi-Fi card (a powerful model, about 25 €). On the first attack, it required expensive equipment and a software specially written to attack iPhones, and on the second one, the author put the device in a Faraday cage to simplify things, while in my case, there is less than 100 € hardware and it works without any special precautions.
The needs
For the equipment: a Raspberry Pi (or any machine running Linux) and a Wi-Fi card compatible with the injection (typically USB RaLink). You can find everything for a relatively low price, the Raspberry Pi at € 25, an SD card, a power supply and a Wi-Fi card for € 10.
For the software: Aircrack-NG, MDK3 (it is there and there to know how to install it). There are even dedicated distributions that directly integrate the tools.
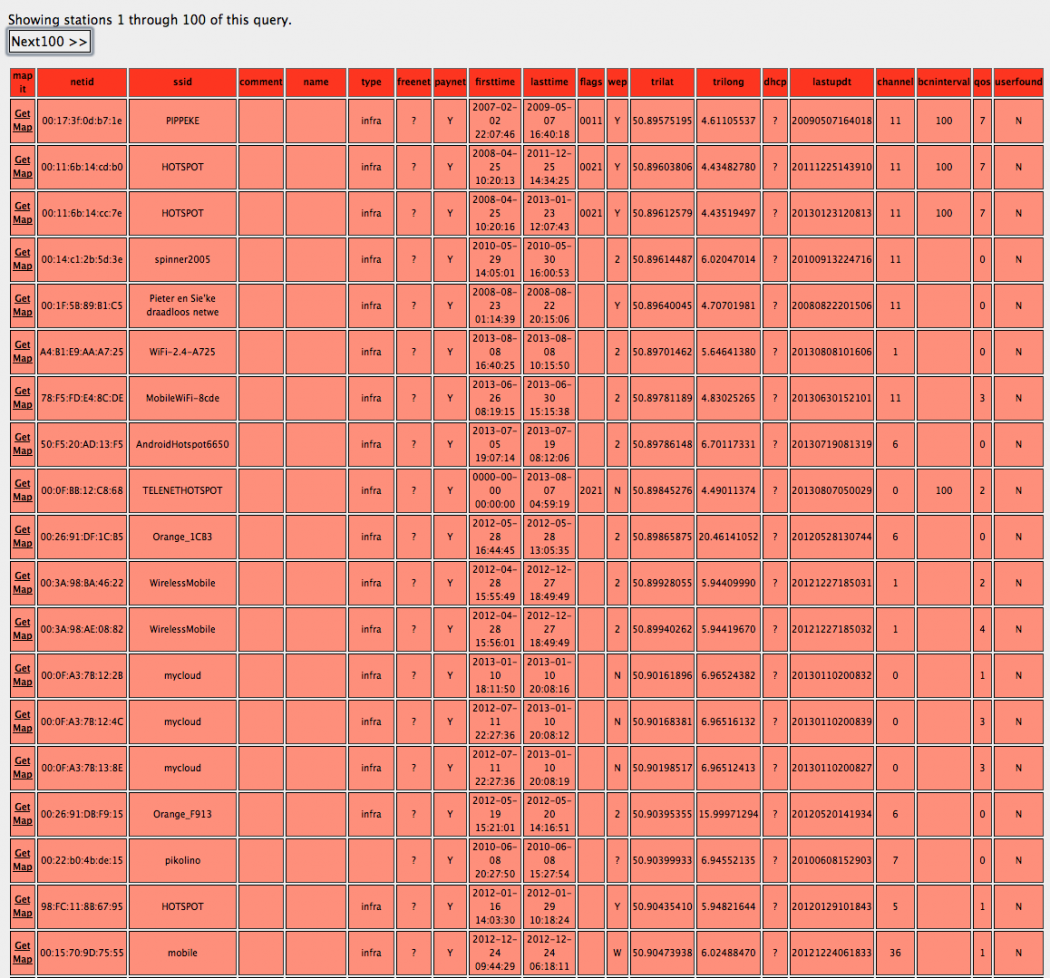
Finally, you need a wireless networks list. There are two solutions: the first is to get to the place you want to simulate (in my case, my workplace) and run a Wi-Fi scan with the Mac OS X diagnostic tool. The second, less precise but more convenient is to use the services of Wigle, a public database of the location of Wi-Fi access points. Just do a search for a place and you will get a list of access points.
Once you get the list, just make a text file containing the MAC access points followed by SSID address. The SSID does not matter, the various databases using only the MAC address. You can set the SSID of your choice, for example to hide your attack. Be careful, if you put a SSID already present, it can cause connection problems.
For example:
aa:bb:cc:dd:ee:ff Free WiFi
bb:cc:dd:ee:ff:aa FBI Van
cc:dd:ee:ff:aa:bb Skynet
Important point: the goal is to distort the location, so it takes a significant number of Wi-Fi networks. In my workplace, I have 25 Wi-Fi networks visible from my Mac, so it needs at least the double for the location to be really distorted (I had to get 65 fake networks to make it work). In my country house, where I pick 6 Wi-Fi networks, it is enough to generate 20 networks to make it work. The attack is much more effective in the fields or in areas where Wi-Fi is rare.
Once we have a test file, just run MDK3 after passing the card in monitor mode. mon0 is the Wi-Fi card, meswifi.txt the file containing the list of networks, -g indicates that we are adding networks on the 11g standard and -t that we are simulating protected networks.
sudo mdk3 mon0 b -v meswifi.txt -g -t
The command will only generate false Wi-Fi networks, that the devices around will see. Be careful not to exceed one hundred networks, some Wi-Fi cards tend to crash if too many networks.
In an area with lots of networks (in the city center, more than 25 networks visible), the efficiency is average, erratic, because the base location is effective. In an area with few networks (my home), the location is distorted within seconds.
The attack works perfectly on all devices that use Wi-Fi to position itself: computers (with the Google or Apple basis), iPod touch, iPad Wi-Fi. It partially works on devices that use a GSM localization (iPhone, iPad 3G, etc..) or a true GPS. With an iPhone, for example, it works indoors in poorly covered areas, but outside, the GPS quickly takes over the wireless location.
The precept of the day is … do not trust the location.